Can Somebody Steal Your Car By Calling It On The Phone?

A team of researchers at UC San Diego and the University of Washington, Seattle, has just published a paper titled “ Comprehensive Experimental Analyses of Automotive Attack Surfaces“. Behind that dry title is a very exciting research study. In essence, they bought a modern reasonably-priced car with lots of fancy features, including a built-in cellular phone interface, and did a serious reverse-engineering exercise to determine whether it had any security vulnerabilities. It’s the most comprehensive study of its kind.
Curiously, you can read their paper all the way through and not see any name of the particular car they studied; they argue these issues apply everywhere. This seems unnecessarily conservative. Besides, if you read their previous paper and look at the photos, any car nut will be able to identify the car without any trouble. Let’s play along anyway; we’ll just say it’s a Generic Motors product.
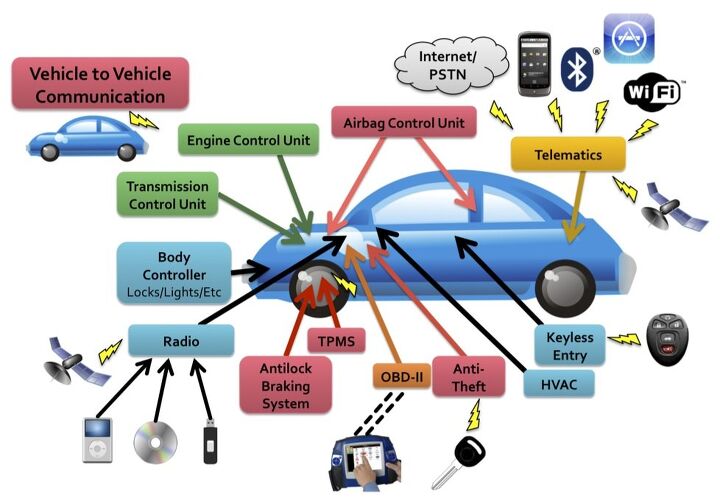
You see, Generic Motors (and, I agree that this is about far more than any one car company) thought it would be really cool to have a telematics system that could do a variety of clever things, like automatically connect an operator to your car when the airbags deploy to ask you whether you’re in need of medical assistance. The way a security person looks at that, though, is that there’s a communications path from the inside of the car out to a data center somewhere and back in again. If the attacker can interpose on that, there’s just no end of mayhem that could be accomplished.
Earlier press reports on this research focused on how they found an attack against the car through the CD player. A carefully constructed CD-ROM, using a malicious compressed music file that would play without issue on your regular PC, could exploit a buffer overflow vulnerability and then control the CD player. Meanwhile, in modern cars, everything’s actually networked together. Consequently, from the compromised CD player, the attacker can take over everything else in the car with the greatest of ease: engine control, door locks, you name it.
Still, that attack is for chumps. How’s a car thief supposed to realistically get a malicious CD into your CD player? Do you valet park your car? No, the really exciting attack, and by exciting I mean “expensive factory recall” exciting, focuses on that built-in cellular phone interface. You see, that means that every Generic Motors car has a phone number and it turns out you can call it. Generic Motors got the security all wrong, and an attacker can thus take over your car without being anywhere physically near it.
What could this evil attacker do? Track you, actuate your brakes, listen in to your conversations, etc. This is normally the stuff that only dystopian science fiction authors dream about. If you want to get seriously dystopian, though, you have to read the paper’s own speculation (page 13). The authors imagine a world where a criminal agency tracks all of the Generic Motors cars in the city. When a garden variety criminal has an hankering for a particular car, he phones up the agency and asks where such a car might be and what it’s owners’ habits are. For a suitable fee, the agency directs the criminal to the car, helpfully unlocks the doors, and starts the engine, all for a modest fee. That’s service with a smile! Similarly, think how much fun the paparazzi could have using similar techniques to eavesdrop on the Hollywood starlet du jour.
Is this just a problem for Generic Motors? Far from it. Virtually any modern car can connect to your phone via Bluetooth and increasingly many cars come with built-in phones. To pick one example, the new Audi A7 uses this to great effect with Google Maps for navigation. To pick another example, Tesla has said that the forthcoming Model S will allow third parties to develop “apps” for their car. What could possibly go wrong with that?
Are our automotive companies and their suppliers responding appropriately? Maybe. I’ve spoken to a number of security people, both in the U.S. and Europe, who consult with these companies. The companies prefer to keep their security concerns under wraps. Suffice to say “they’re working on it.”
[Disclosure, I was the “shepherd” for this paper, meaning that the USENIX Security conference program committee asked me to help the authors of the paper make the changes that the committee requested. I’m not a co-author of the paper and I have had not personally participated in any automotive security analyses, unless you count the time, in high school, that we discovered that my Nissan key worked perfectly in a friend’s Mazda. Zoom zoom.]

More by Dan Wallach
Latest Car Reviews
Read moreLatest Product Reviews
Read moreRecent Comments
- Lou_BC Well, I'd be impressed if this was in a ZR2. LOL
- Lou_BC This is my shocked face 😲 Hope formatting doesn't fook this up LOL
- Lou_BC Junior? Would that be a Beta Romeo?
- Lou_BC Gotta fix that formatting problem. What a pile of bullsh!t. Are longer posts costing TTAC money? FOOK
- Lou_BC 1.Honda: 6,334,825 vehicles potentially affected2.Ford: 6,152,6143.Kia America: 3,110,4474.Chrysler: 2,732,3985.General Motors: 2,021,0336.Nissan North America: 1,804,4437.Mercedes-Benz USA: 478,1738.Volkswagen Group of America: 453,7639.BMW of North America: 340,24910.Daimler Trucks North America: 261,959


































Comments
Join the conversation
Back in the 70's there were only 24 unique keys for the Honda 750 (the gun sportsbike of it's day). A friend of mine had one, but I declined his offer of free use of his spare key so I could "acquire" one of my own.
Wireless Mobile phones connectivity is a better option, but it can be a harmful for us because if your mobile will steal than your car is in the danger. Now a day's many cars having so many security options, and it will be increasing for more secure future of us and our cars.