#Security
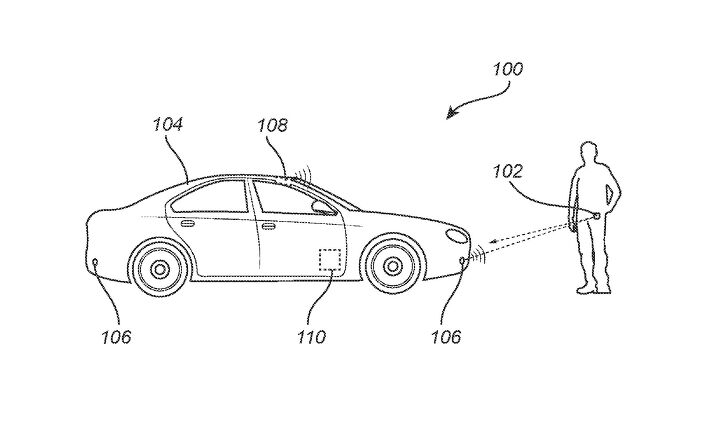
Volvo Patents New Tool to Combat Car Thieves
Volvo has reportedly filed a new patent with the United States Patent and Trademark Office (USPTO) that would add digital protections designed to prevent modern car thieves from doing what they do. While the golden age of car thievery typically involved criminals skulking around in the dark to find an isolated model they could jimmy open and then hot-wire, today’s thieves tend to linger in crowded parking areas our outside homes with computers that scan and capture the codes being transmitted remotely from the key fob to the car.
Dodge Introduces Three Horsepower Challenger, Charger
Dodge has long been synonymous with high levels of horsepower. Modern-day marketing materials practically scream it into your ear, acknowledging the company’s historic penchant for providing ludicrous amounts of power for hysterically low prices. The reality is a bit more complicated, however. While Mopar brands were indeed offering some of the best bang-for-your-buck muscle cars, back when they were a tad more novel, some of the fastest machines actually came from General Motors and Ford.
Today’s situation is very much the same. When the rest of the industry started downsizing powertrains, Dodge was still trying to squeeze even more juice from its colossal V8 engines — installing them anywhere they might fit. Rivals quickly got wise to its attempt to corner a segment just about everyone else had abandoned, resulting in gems like the Chevrolet Camaro ZL1 or Ford Shelby GT500. But with everyone now back on board with the concept of displacement meaning power, Dodge has decided to change tactics.
What if it manufactured the V8 offering the smallest amount of horsepower imaginable?
Report: Chinese Military Bans Tesla Vehicles From Facilities
The Chinese military has decided to ban all Tesla vehicles from housing complexes and bases after citing them as a potential security risk. Since the cars use an array of ultrasonic sensors and cameras to create a panoramic view used for advanced driving features, China is concerned the American brand could use the cars to covertly map out sensitive areas.
Tesla's Cameras Can Catch Vandals Defacing Your Car, but Not Drivers Nodding Off
Sentries stand on guard for our safety, keeping watch over sleeping or unprotected persons, and Tesla’s “Sentry Mode” system pretty much does the same. While two-legged assailants can’t slip a Fairbairn-Sykes dagger between the digital guardian’s ribs to disable the feature, the external camera security system can, in return, set that assailant up for a date with the police.
That’s what happened when one Tesla went up against an angry Coloradoan.
Hackers Digitally Invade Tesla Model 3, Winning One
Computer experts successfully broke a Tesla Model 3 at the “Pwn2Own” hacking event held recently in Vancouver. However, Tesla Motors isn’t biting its nails over someone finding vulnerabilities in its system, as it was privy to the plan. The automaker has operated a “bug bounty program” for the past 4 years, rewarding anyone who can pull it off — going so far as saying it wouldn’t void a vehicle’s warranty if a customer successfully hacked it in “good faith.” It even offered a maximum reward of $15,000 (USD) last year.
Meanwhile, the group that managed to break the Model 3 in Canada this month received more than a sack of cash from the automaker.
At What Point Do We Want Our Cars to Be Less Like Our Phones?
That’s one of the unspoken questions contained in Automotive News‘ report on automotive supplier Continental’s new biometric authentication technology. Passwords are the scourge of the modern age, it’s true, and having a secure way of locking and unlocking a sensitive…anything…is preferable to trying to remember that damn combination of letters and numbers.
Computer files. Your phone. The entrance to sterile, high-security office buildings. These are all good candidates for facial recognition technology, fingerprint and retina scans, or voice recognition. But your car? It’s true that using this technology — in addition to conventional keys and fobs — would add an extra layer of defence, improving your vehicle’s chances of remaining unmolested. But at what cost?
Does This Ford Patent Spell the End of the Door Keypad?
Ford’s electronic keypad is a delightful throwback to the days when drivers would proudly unlock their new Town Car by punching in a code on the window sill, or just below the door handle.
However, a Ford patent published by Autoblog raises the possibility that the automaker might do away with the time-honored feature.
Fiat Chrysler Cracks Down on Data Violators After Ram/Jeep Theft Ring Bust
A Houston-area vehicle-theft ring that used laptops to enter, then steal, over 100 Jeep and Ram vehicles exposed a serious internal security breach at Fiat Chrysler Automobiles.
Now that two arrests have been made in the case, FCA is talking tough and threatening criminal proceedings against anyone who provides outsiders with key vehicle data, Automotive News reports.
Attention: Password Reset Sufferers
Ever since a data breach left user accounts vulnerable to attack a couple of months ago, VerticalScope has been going through each one of its properties and resetting user passwords.
Normally, this reset would result in an email being sent to the user notifying them of that fact. However, some of our more prolific members have decided to provide email addresses that simply don’t exist.
I’m here to help.
If you’d like to access your commenter account once again, here’s what to do:
100 Million Volkswagen Group Vehicles Can Be Unlocked With a Cheap Hacking Device
Two decades’ worth of Volkswagen Group vehicles are vulnerable to a simple, cheap hack that can unlock their doors.
A research paper released this week (first reported by Wired) describes how multiple Volkswagen, Audi, Seat and Skoda models built since 1995 can be unlocked using a handmade radio that copies key fob signals.
Fiat Chrysler Will Give You Cash to Find Cyber Threats
In a few weeks, after Pokémon Go jumps the shark and we all head back to our homes for nights of solitude, Fiat Chrysler Automobiles will offer another opportunity for high-tech geekery. And a lucrative one, too.
Announced today, the automaker will hand tech-savvy individuals cold, hard cash in return for information on weaknesses in its vehicles’ cybersecurity. Exposing a hidden backdoor that hackers could sneak through will net you up to $1,500.
Voyeur Edition? The Cadillac CT6 is Ready to Record Your Private Moments
You just know this feature is going to be used by a frisky couple or a penniless college film student with a traditional, “buy domestic!” uncle.
Cadillac made a big deal about the video rear-view mirror in its 2016 CT6, but now it says drivers can film — and store— video shot by four external cameras. With the range-topping sedan now rolling into dealers, the automaker really wants people to know just what the industry-first system can do.
Don’t lose that memory card if you’re an adventurous driver.
NSA in Your NSX: Your Car is a Data Breach Waiting to Happen
Your faithful four-wheeled companion — the one that costs you an arm and a leg but you still love it — has the data-gathering potential to make your life a Kafkaesque nightmare.
Researchers have found that a car’s computer network can identify a driver just by the way they operate the vehicle. Even something as simple as the brake pedal can pinpoint who’s behind the wheel, according to a report published in Wired.
Stupidity, Laziness Are Connected Car Security's Weak Links
My email address is dwallach@gmail.com, and this XKCD comic is a very real part of my life. Others confuse me for all sorts of other Wallachs out there in the world. I’ve been invited to bachelorette parties in New York, received electronic court filings from Florida, and recently I got something new: an email welcoming me to my new Lexus that invited me to take part in exclusive consumer surveys.
Of course, I didn’t recently purchase a Lexus, and there was no “hey, wrong email address” button anywhere to be found. So what did I do? I “forgot” my password, logged in to someone else’s Lexus account, and figured out who actually owned the Lexus. After all, they’d probably want to know.
Now ISIS Wants Into the Self-Driving Car Business
Don’t expect ride sharing.
It seems, some days, that everyone and their sister is working on autonomous vehicles, but a NATO security expert just confirmed that even ISIS is getting in on the technology, Britain’s Express newspaper reports.
Not interested in giving drivers a chance to stretch out while returning emails, Islamic State militants are instead planning a much more sinister (and very predictable) use for their self-driving cars.




























Recent Comments